Published to clients: March 10, 2026 ID: TBW2074
Published to Whisper Club: March 10, 2026
Analyst(s): Dr. Doreen Galli
Photojournalist(s): Dr. Doreen Galli
Abstract:
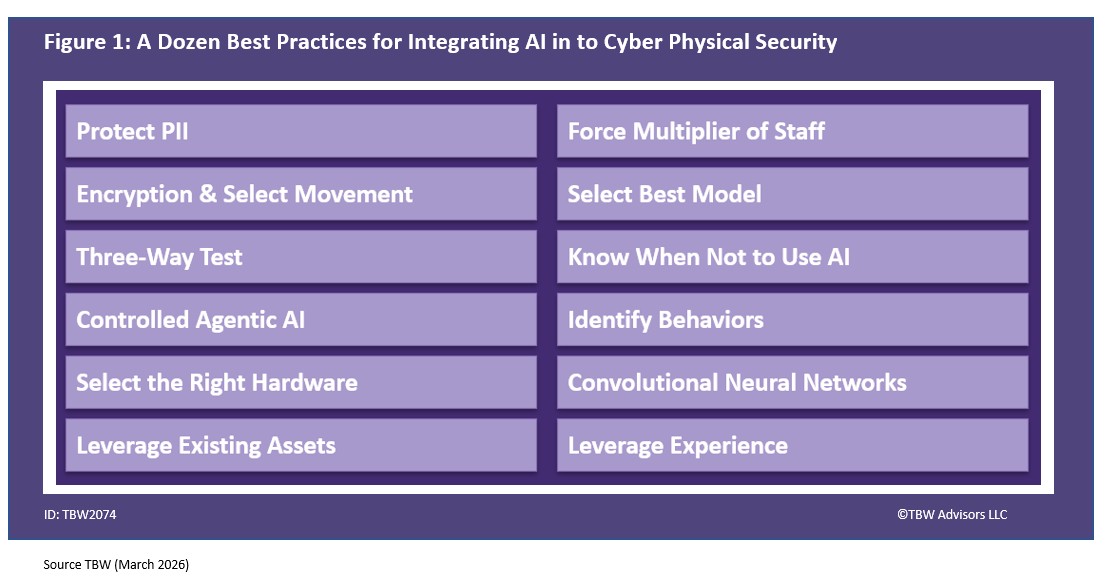
“This Whisper Report address the question regarding the best practices for integrating AI and ML into our security Systems. It highlights how leaders emphasize protecting PII, using selective data movement, optimizing hardware, choosing the right models, and knowing when AI should not be applied. Insights come from LVT’s Steve Lindsey, Safr’s John Cassise, 360 Privacy’s Trinity Davis, Intel’s Mike Nielsen, RightCrowd’s Jason Bohrer, Bioconnect’s Edsel Shreve, Vaidio’s Marshall Tyler, and Databuoy’s Kathleen Griggs. “
Analysis available only to clients at this time. Join the YouTube Whisper Club at the Whisper Club Level to get access to the video edition today.
Related playlists
- Industry Whispers: Public is Private – Confidential Computing in the Cloud | TBW ADVISORS
- Conference Whispers: Black Hat USA 2019
- Whisper Report: How can we enhance our cybersecurity measures to protect against emerging Cyber Physical threats?
- Conference Whispers: ISC West 2025
- Conference Whispers: Identiverse 2025
- Playlist for Whisper Report: What are the best practices for integrating AI and machine learning into our security systems?
Corporate Headquarters
2884 Grand Helios Way
Henderson, NV 89052
©2019-2025 TBW Advisors LLC. All rights reserved. TBW, Technical Business Whispers, Fact-based research and Advisory, Conference Whispers, Industry Whispers, Email Whispers, The Answer is always in the Whispers, Whisper Reports, Whisper Studies, Whisper Ranking, The Answer is always in the Whispers, and One Change a Month, are trademarks or registered trademarks of TBW Advisors LLC. This publication may not be reproduced or distributed in any form without TBW’s prior written permission. It consists of the opinions of TBW’s research organization which should not be construed as statements of fact. While the information contained in this publication has been obtained from sources believed to be reliable, TBW disclaims all warranties as to the accuracy, completeness or adequacy of such information. TBW does not provide legal or investment advice and its research should not be construed or used as such. Your access and use of this publication are governed by the TBW Usage Policy. TBW research is produced independently by its research organization without influence or input from a third party. For further information, see Fact-based research publications on our website for more details.