Published to Whisper Club: June 9, 2026 ID: TBW2081
Analyst(s): Dr. Doreen Galli
ABSTRACT:
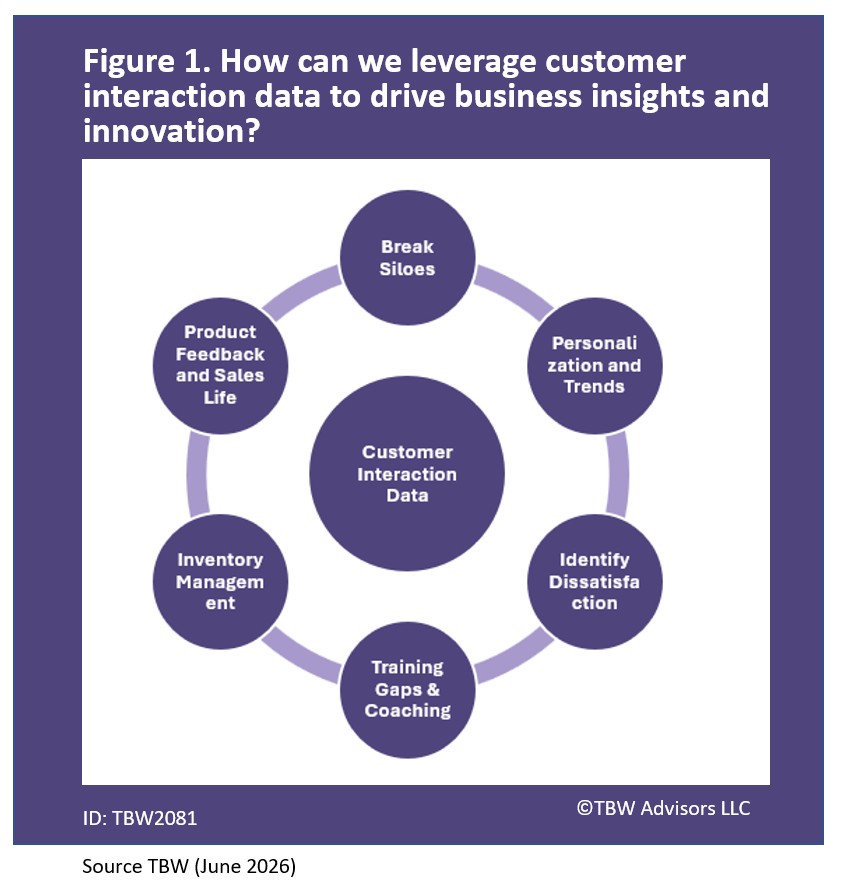
“This Whisper Report investigates how can we leverage customer interaction data to drive business insights and innovation. Based on expert perspectives gathered at Customer Connect Expo held in Las Vegas, teasing how everyday conversations can become enterprise-wide signals—before the best opportunities and risks surface on their own. Cited experts: Siva Kannan Ganesan Macy’s, Dr. Kalifa Oliver at Ford, Sean Gigremoss at Claritiv, Atul Grover at Enthu.ai, Dayna Neumann at Unified Direct Solutions, Pedro Lopez Slevin at Mitrol, Alex Hamberger at Blitz, Zac Brooksher at Verse.ai and Patrick Reynolds Etech.”
Analysis available only to clients at this time. Join the YouTube Whisper Club at the Whisper Club Level to get access to the video edition today.
Related playlists
- Whisper Report: How can we integrate AI-driven customer service solutions with our existing IT infrastructure?
- Whisper Report: What are the most effective strategies for ensuring data security and privacy in customer interactions?
- Whisper Report: How can we leverage customer interaction data to drive business insights and innovation?
- Conference Whispers: Customer Connect Expo 2025
- Conference Whispers: Customer Connect Expo 2025 (the report)
Corporate Headquarters
2884 Grand Helios Way
Henderson, NV 89052
©2019-2026 TBW Advisors LLC. All rights reserved. TBW, Technical Business Whispers, Fact-based research and Advisory, Conference Whispers, Industry Whispers, Email Whispers, The Answer is always in the Whispers, Whisper Reports, Whisper Studies, Whisper Ranking, Whisper Club, Whispers, The Answer is always in the Whispers, Vegas Convention Library, and One Change a Month, are trademarks or registered trademarks of TBW Advisors LLC. This publication may not be reproduced or distributed in any form without TBW’s prior written permission. It consists of the opinions of TBW’s research organization which should not be construed as statements of fact. While the information contained in this publication has been obtained from sources believed to be reliable, TBW disclaims all warranties as to the accuracy, completeness or adequacy of such information. TBW does not provide legal or investment advice and its research should not be construed or used as such. Your access and use of this publication are governed by the TBW Usage Policy. TBW research is produced independently by its research organization without influence or input from a third party. For further information, see Fact-based research publications on our website for more details.