Published to Readers: December 10, 2025 ID: TBW2110
Whisper Club Release: December 10, 2025
Public and Video Release: February 24, 2026
Analyst(s): Dr. Doreen Galli
Photojournalist(s): Dr. Doreen Galli
Abstract
“This Whisper Report investigates the biggest 5G myth tech leaders still believe. Insights from MWC Las Vegas reveal why common assumptions—like 5G being only about bandwidth, too costly, or reserved for telecom giants—are wrong. These misconceptions can stall innovation and strategy. Explore how 5G is enterprise-ready, cost-effective, and far more transformative than most expect. If your roadmap relies on outdated beliefs, this report will challenge and reshape your perspective.”
Enjoy the related Computer Talk Radio broadcast.
Target Audience Titles:
- Chief Information Officer (CIO), Chief Technology Officer (CTO), Chief Digital Officer (CDO), VP of Network Engineering, VP of IT Infrastructure, Head of Enterprise Architecture, Director of Mobility & Wireless Strategy
- Enterprise Network Architect, Wireless Systems Engineer, IT Infrastructure Engineer, Mobility Solutions Specialist, Telecom Integration Engineer, Cloud & Edge Computing Engineer
Key Takeaways
- 5G delivers far more than bandwidth—it enables future-proofing and advanced capabilities critical for enterprise innovation.
- Private 5G is cost-effective, often cheaper than traditional wireless, and offers unique advantages over Wi-Fi.
- 5G is enterprise-ready today, with deployment and management as simple as traditional IT networks
What’s the biggest 5G myth tech leaders still believe?
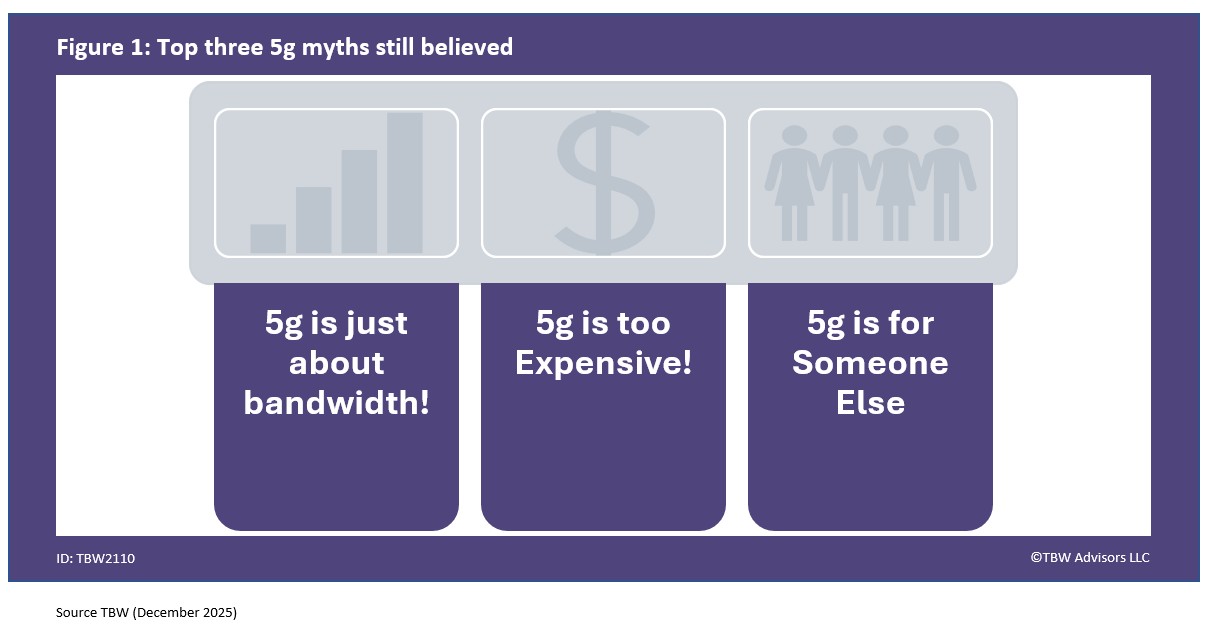
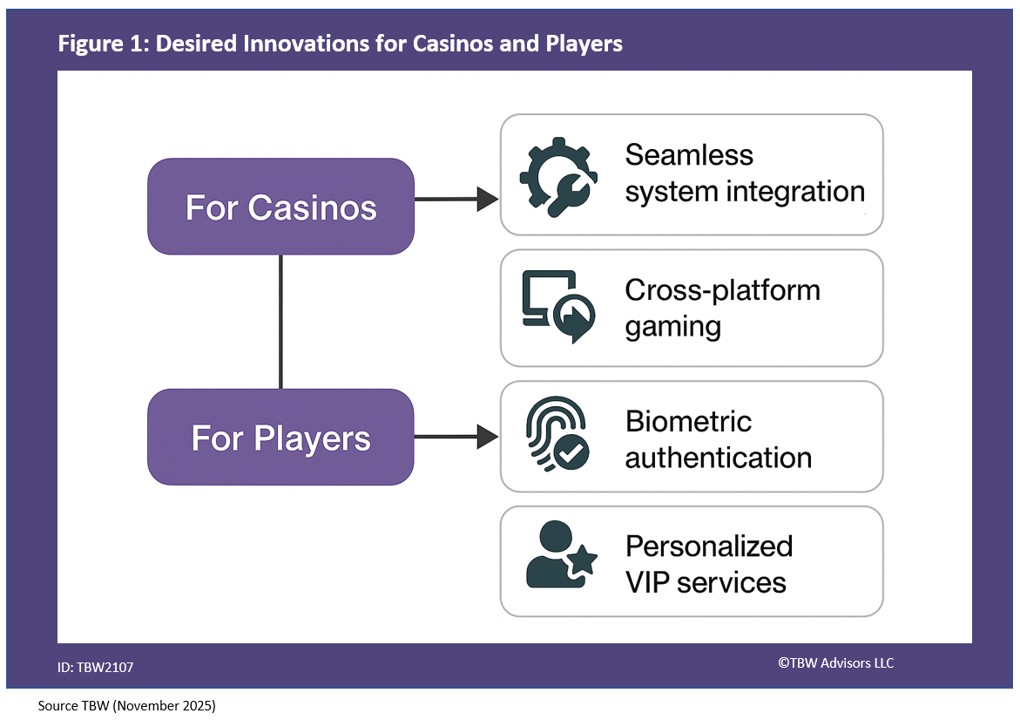
We took the most frequently asked and most urgent technology questions straight to the mobility and wireless experts gathering at the MWC Las Vegas held at the Fontainebleau. This Whisper Report addresses the question regarding the biggest 5G myth tech leaders still believe as depicted in Figure 1.
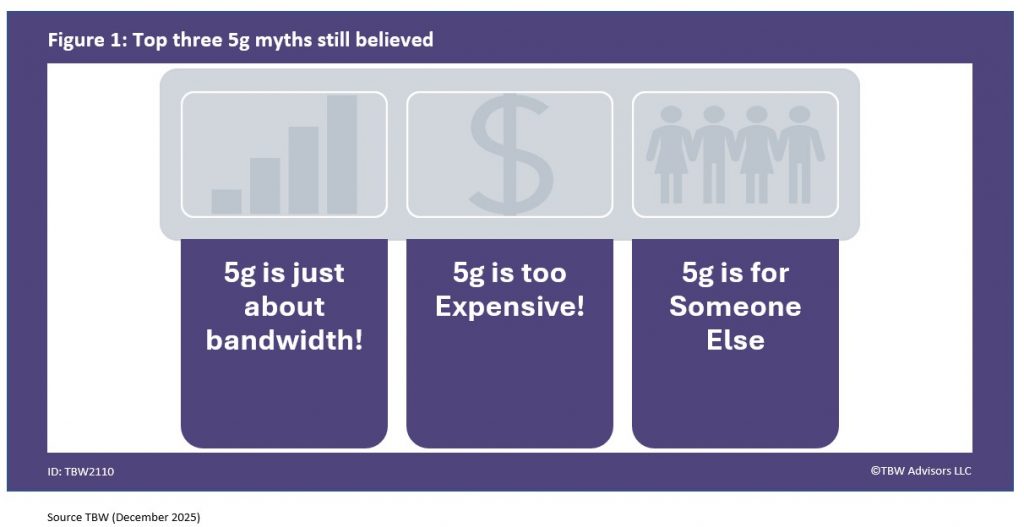
Our first myth comes from GetWireless’ Kalpit Kadia, “5G is more like a throughput requirement than future proofing.” If you believe the only thing 5g brings to the table is bandwidth you are missing it. Kalpit continued. “So it’s not all about through requirement. It’s you know also to do with future proofing your product because as network infrastructure is changing by different carriers, it’s a good idea to move to a 5g stack technology which is going to be here around here for a long time.” Remember when you enable 5g in our organization you empowered it with more than just bandwidth, you enabled all the capabilities that come with 5g beyond the bandwidth.
5g is too Expensive!
The next myth is a critical one particular for those building out wireless infrastructure in public spaces. Baicells’ Minchul Ho argued that the biggest myth is, “the cost or differentiation from Wi-Fi.” Minchul elaborated further. “There’s a huge upside to 5G that you cannot get with any other wireless technologies at about the same price if not half the cost of what traditional wireless system would take.” If you are working on your business justification for 5g expansion in your organization, be sure to schedule an inquiry with your analyst at TBW Advisors LLC. We can review not only your strategy and roadmap, but help ensure the major use cases in your organization have been captured to ensure maximum business impact.
5g is for Someone Else
Perhaps the biggest myth of all is brought to us by Canoga Perkins’ Siddharth Khattar. “That private 5G is still seen by many as a telecom only technology. Something that is hard to roll out, something that is hard to administer across your enterprise networks and comes with enterprise environments and therefore comes with a lot of expense and it’s always a technology for somebody else.” The reality is 5g is enterprise ready and is not just for telecoms for tech giants. Even more important is the easy of deployment and management as Siddharth explains further. “What we are doing the truth is that today’s private 5G networks can be administered and managed much more like IT and enterprise that people that CIOS and organizations are used to doing. Be able to administer and manage that as easily as you would a as easily as you would your traditional IT networks today with so much more functionality than what they deliver today.”
In conclusion, 5g is about so much more than the bandwidth, is cost effective, and is ready today for you to deploy in your organization.
Related playlists and Publication
- Whisper Report: How will edge AI reshape enterprise architecture?
- Whisper Report: What mobile tech trend will blindside CIOs next?
- Whisper Report: What’s the best part about attending MWC live in Vegas?
- Conference Whispers: MWC Las Vegas
Corporate Headquarters
2884 Grand Helios Way
Henderson, NV 89052
©2019-2025 TBW Advisors LLC. All rights reserved. TBW, Technical Business Whispers, Fact-based research and Advisory, Conference Whispers, Industry Whispers, Email Whispers, The Answer is always in the Whispers, Whisper Reports, Whisper Studies, Whisper Ranking, The Answer is always in the Whispers, and One Change a Month, are trademarks or registered trademarks of TBW Advisors LLC. This publication may not be reproduced or distributed in any form without TBW’s prior written permission. It consists of the opinions of TBW’s research organization which should not be construed as statements of fact. While the information contained in this publication has been obtained from sources believed to be reliable, TBW disclaims all warranties as to the accuracy, completeness or adequacy of such information. TBW does not provide legal or investment advice and its research should not be construed or used as such. Your access and use of this publication are governed by the TBW Usage Policy. TBW research is produced independently by its research organization without influence or input from a third party. For further information, see Fact-based research publications on our website for more details.