Published to clients: August 4, 2025 ID: TBW2080
Published to Readers: August 5, 2025
Published to Email Whispers: TBD
Public and Video Release: TBD
Analyst(s): Dr. Doreen Galli
Photojournalist(s): Dr. Doreen Galli
Abstract:
“Effective strategies for securing customer data include encryption at rest, in transit, and during compute; cautious AI adoption; and strict access controls. Removing or masking personally identifiable information (PII) and training staff on cybersecurity best practices are essential. Legal compliance, intellectual property protection, and customer trust drive the need for robust privacy measures in customer interactions.”
What are the most effective strategies for ensuring data security and privacy in customer interactions?
We took the most frequently asked and most urgent technology questions straight to the technologists gathering at Customer Connect Expo 2025 held at the Las Vegas Convention Center. This Whisper Report addresses the question regarding What are the most effective strategies for ensuring data security and privacy in customer interactions? There are two reasons security and privacy are critical in this space. As Ford’s Dr. Kalifa Oliver pointed out, “to first really understand the laws..” In fact, all governance program definitions start with legal requirements, then industry regulations and requirements, then internal privacy promises made to customers. The second critical reasons for ensuring data security and privacy as Claritiv’s Sean Gigremoss reminds us, “your knowledge for your business comes from all the conversations that you’re having – that is your IP (intellectual property).”
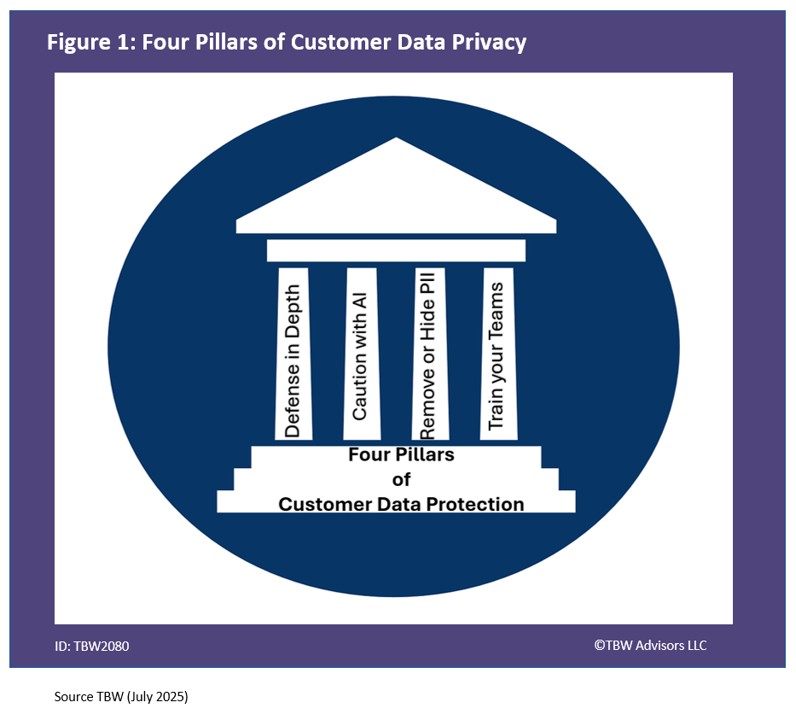
Figure 1. Four Pillars of Customer Data Protection
Defence in Depth
As Macy’s Siva Kannan Ganesan pointed out, “all those regulation and implementing an regulation it’s a multi-step approach like data and motion data at rest should be encrypted and you have to make sure it’s like the access strict access control and frequent evaluation of the data breach.” With security depth is always valuable. TBW Advisors LLC advises clients to not only use encryption at rest and in transit, but to leverage protections during compute leveraging Confidential Computing. For additional research, enjoy Industry Whispers: Public is Privacy – Confidential Computing in the Cloud available on TBW Advisors YouTube Channel.
Caution with AI technologies
TBW Advisors has frequently warned if you are not being charged for the product, you are the product. If you are the product, you should assume you do not have privacy. Today with many of the advanced AI products, even lower tier paid products do not get privacy; rather they are being used to further train the product. As Ford’s Dr. Kalifa Oliver observed, “you really got to start asking organizations that have AI technologies about their Blackbox about how the data is being trained. You have to ask them about data breaches you have to be conservative about how you implement things because I think the law is going to catch up and the hardest thing to do is trying to go back and fix it.”
Remove or Hide PII
One critical step to ensure privacy is to not send PII or personally identifiable information to tools. Enthu.ai’s Atul Grover denoted, “we also ensure that we deduct the PI information we deduct almost 16 kind of PIs including social security data birth credit card information …. we do that in the recording as well as all the analytics.” While removing the information is a common practice, masking data is also quite common. As Mitrol’s Pedro Lopez Slevin shared, “our banks for example you will probably have on premise data servers. Everything will be with TLS 1.2 two or higher you know and create your data. We’re talking about AI, we usually do rack so you will have to process every information into embeddings and those embeddings are..unreadable if you just put it in a vector database.”
Train your Teams
While the term Human in the Loop has gained popularity with generative AI and agentic solutions, cybersecurity has always known the human in the loop as being a critical risk factor. Thus in order to truly ensure data security and privacy, you must train those humans! Randy Simmons from FaxSipIt shared the common journey towards compliance. “we’ve gone through a HIPPA audit and we’re secure there we just finished the SOC 2 audit and we’re SOC 2 compliant so people have come in they’ve audited our system our policies they’ve come with recommendations or not and we pass the audit for the socks 2 audit so our staff all goes through cyber security training as well we go through a wiser cyber security training and then also we send phishing to our to our employees and see if they’re going to click and if they click on a link then guess what they’re doing they’re doing that training all over Again.” So remember, do not click on that link without checking the link is safe first!
Related playlists and References
- Whisper Report: How can we integrate AI-driven customer service solutions with our existing IT infrastructure
- Conference Whispers: Customer Connect Expo 2025
- Whisper Report: What are the most effective strategies for ensuring data security and privacy in customer interactions?
- Playlist – Whisper Report: What are the most effective strategies for ensuring data security and privacy in customer interactions?
Corporate Headquarters
2884 Grand Helios Way
Henderson, NV 89052
©2019-2025 TBW Advisors LLC. All rights reserved. TBW, Technical Business Whispers, Fact-based research and Advisory, Conference Whispers, Industry Whispers, Email Whispers, The Answer is always in the Whispers, Whisper Reports, Whisper Studies, Whisper Ranking, The Answer is always in the Whispers, and One Change a Month, are trademarks or registered trademarks of TBW Advisors LLC. This publication may not be reproduced or distributed in any form without TBW’s prior written permission. It consists of the opinions of TBW’s research organization which should not be construed as statements of fact. While the information contained in this publication has been obtained from sources believed to be reliable, TBW disclaims all warranties as to the accuracy, completeness or adequacy of such information. TBW does not provide legal or investment advice and its research should not be construed or used as such. Your access and use of this publication are governed by the TBW Usage Policy. TBW research is produced independently by its research organization without influence or input from a third party. For further information, see Fact-based research publications on our website for more details.